telanova blog
telanova: the outsourced IT team that feels like your own.
Keep up to date with the latest news and articles from the world of IT and telanova. Providing advice, consultancy, helpdesk, monitoring and maintenance, updates, upgrades, security: all the things your in-house team would do, but better and at a fraction of the cost and hassle.
How Managed IT Services Can Save Your Small Business Time & Money
By Telanova | 18 June 2025
Outsourced IT Helpdesk vs. In-House Support: Which is Right for Your Business?
By Telanova | 11 June 2025
Why you should ensure your laptops and other mobile devices are encrypted
By Telanova | 23 October 2024
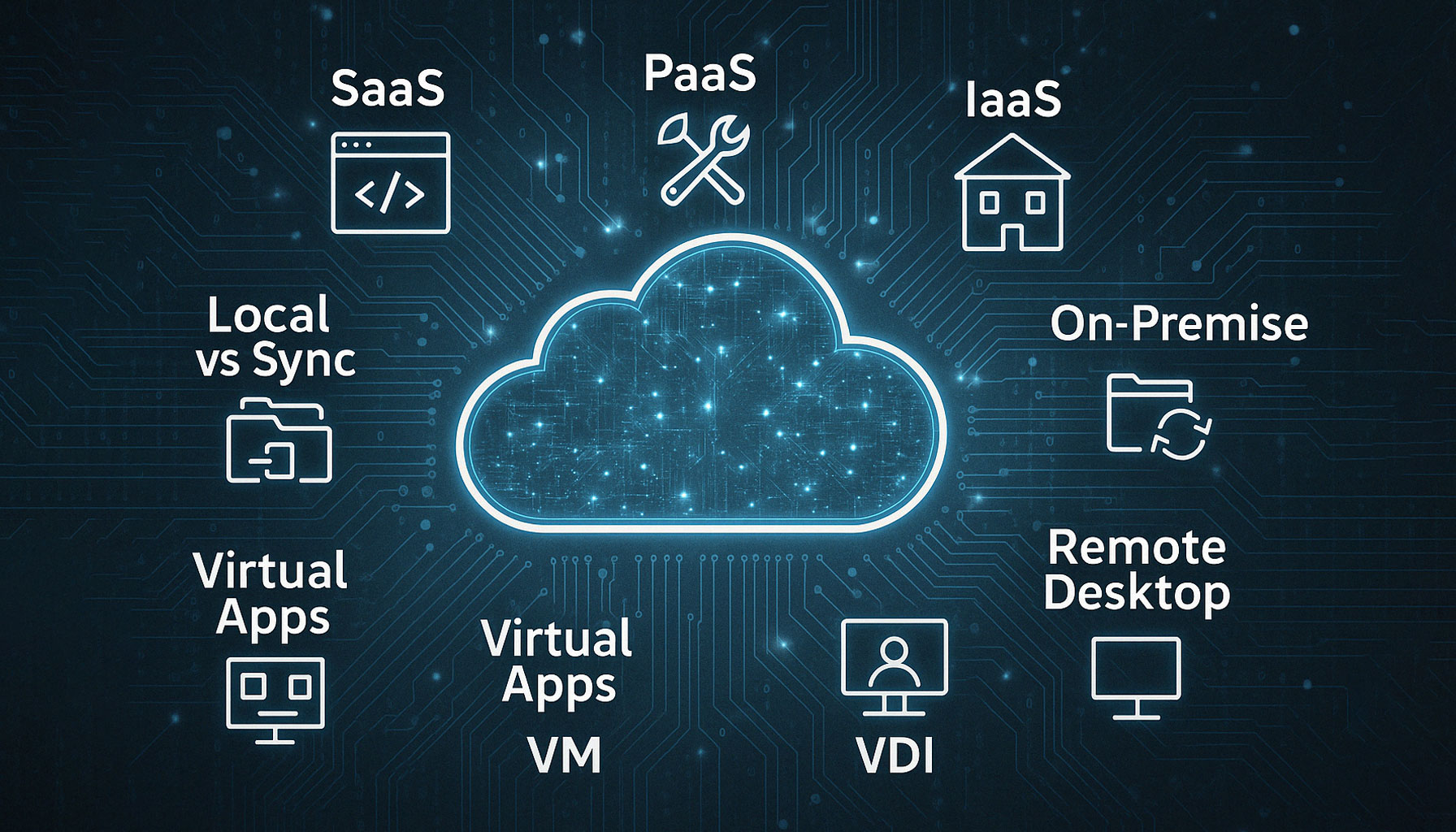
Case Study: Migrating from Cloud Remote Desktop to Pure SaaS for an Ascot-Based Business
By Telanova | 25 September 2024
WiFi or wired connections - How to get the best for your organisation?
By Telanova | 22 May 2022
Discover if WiFi or wired connections is the best for your organisation?Bring Your Own Device safely
By Telanova | 14 March 2022
Discover how to safely enable staff to bring their own devices.