telanova blog
telanova: the outsourced IT team that feels like your own.
Keep up to date with the latest news and articles from the world of IT and telanova. Providing advice, consultancy, helpdesk, monitoring and maintenance, updates, upgrades, security: all the things your in-house team would do, but better and at a fraction of the cost and hassle.
Case Study: Empowering a Financial Services Spin-Off with Independent IT Infrastructure
By Telanova | 04 March 2026
How We Support Microsoft 365 for Our Clients: Teams, SharePoint & OneDrive
By Telanova | 28 January 2026
How Can I Link a Printer to Everyone’s Computer? A Practical Guide for Small Businesses
By Telanova | 21 January 2026
Microsoft 365 vs Google Workspace: What’s the Difference for Small Businesses?
By Telanova | 14 January 2026
2026 New Year Resolutions for Smarter, Safer, and More Resilient IT
By Telanova | 07 January 2026
Managed IT vs Break-Fix: Which IT Support Model Helps Your Business Grow?
By Telanova | 03 December 2025
How to Repair the EFI Bootloader on a GPT Hard Drive for Windows
By Telanova | 26 November 2025
Keeping Your Devices Secure: A Guide to Cyber Security, Device Compliance, and Intune Auto-Updates
By Telanova | 19 November 2025
Translating Business Continuity and Disaster Recovery IT Jargon
By Telanova | 12 November 2025
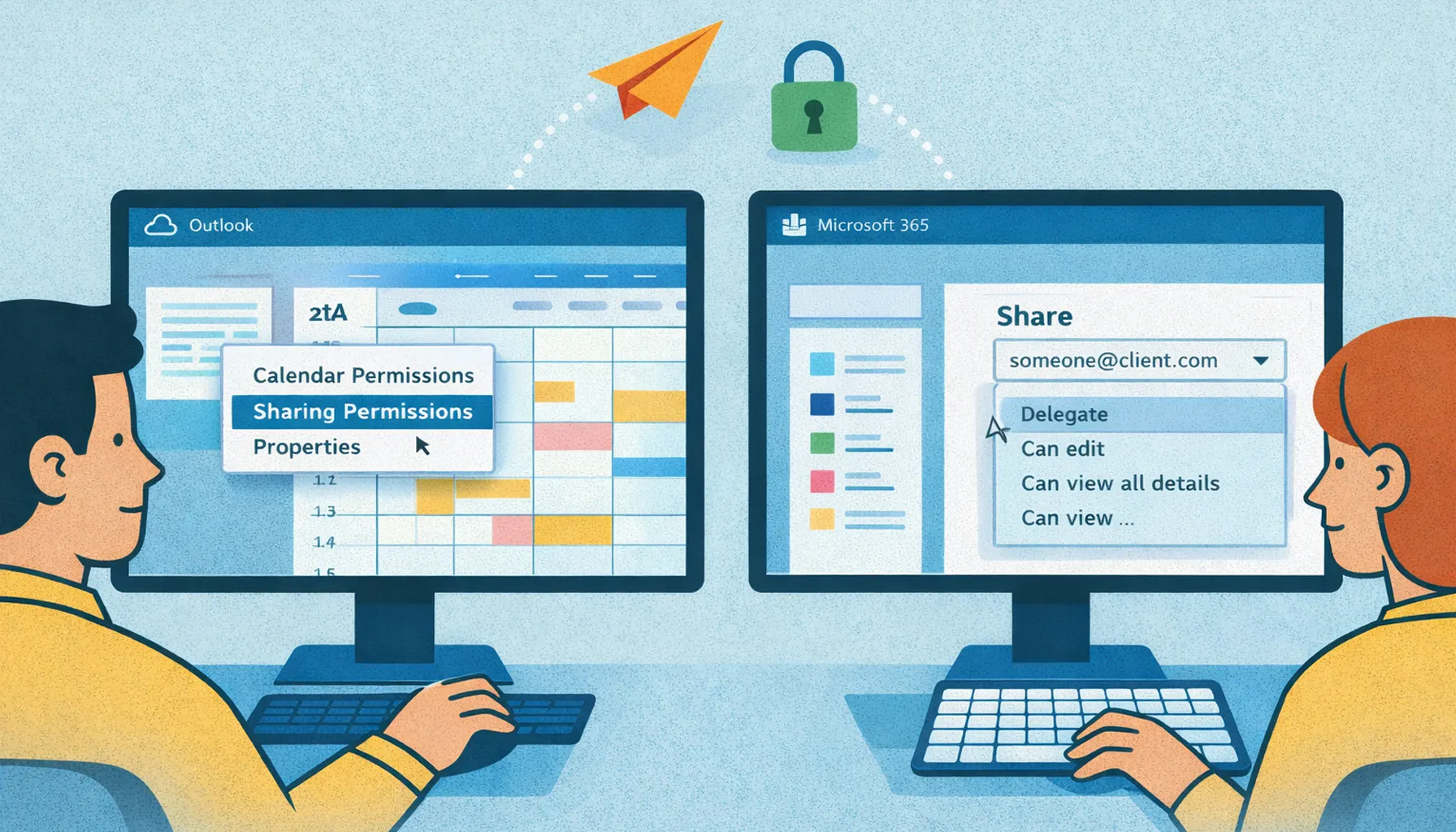
Managing Microsoft 365: User Administration and Exchange Online Support
By Telanova | 05 November 2025
Discover Microsoft Forms: A Hidden Microsoft 365 Tool for Surveys & Feedback
By Telanova | 22 October 2025
Wired vs. Wireless Network Connections in the Workplace: What's Best for You?
By Telanova | 15 October 2025
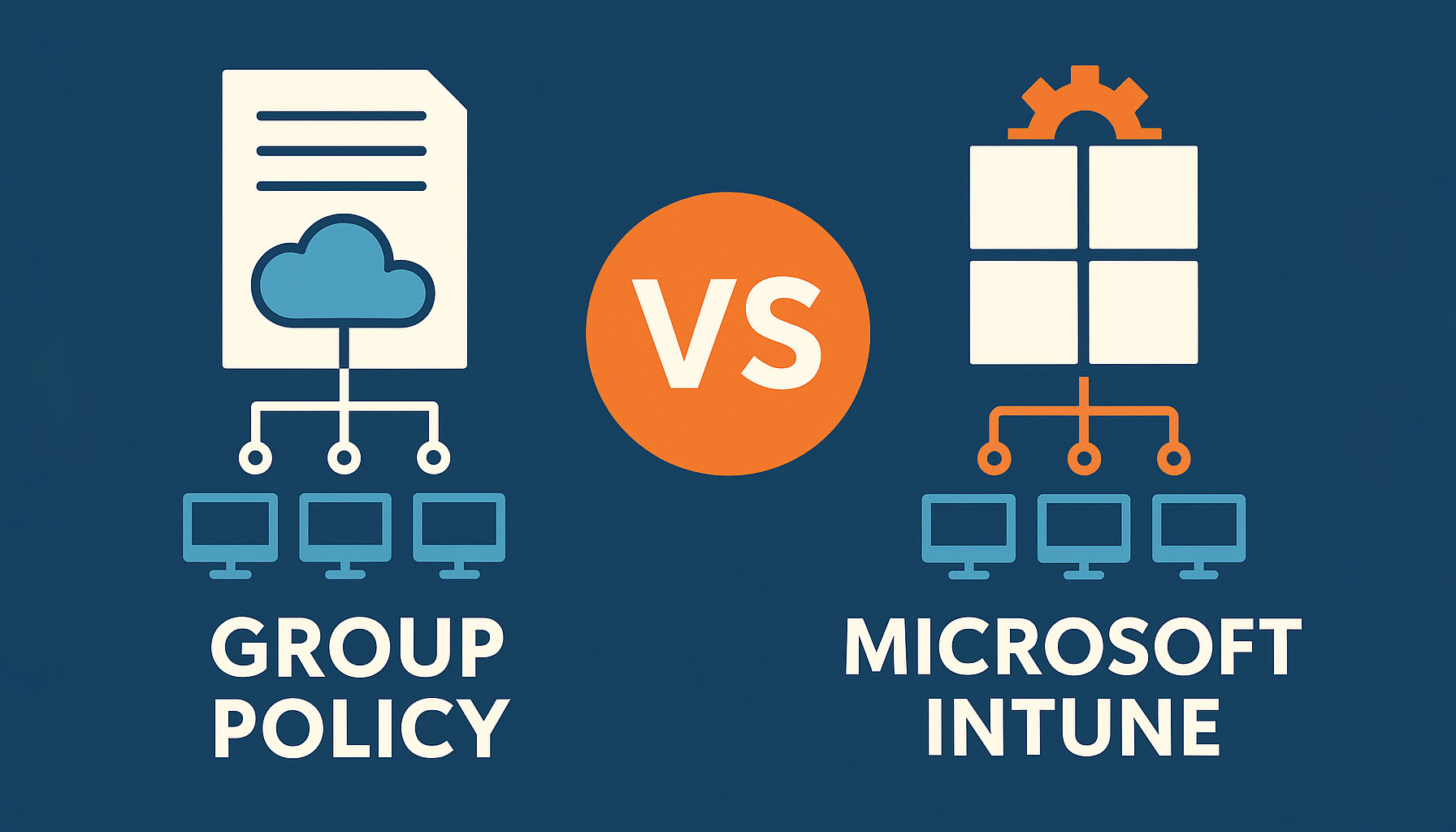
How To: Deploying Software to Multiple Devices - Group Policy vs. Microsoft Intune
By Telanova | 17 September 2025
Why Monitoring Risky Sign-ins in Microsoft 365 is Essential for Your Business
By Telanova | 10 September 2025
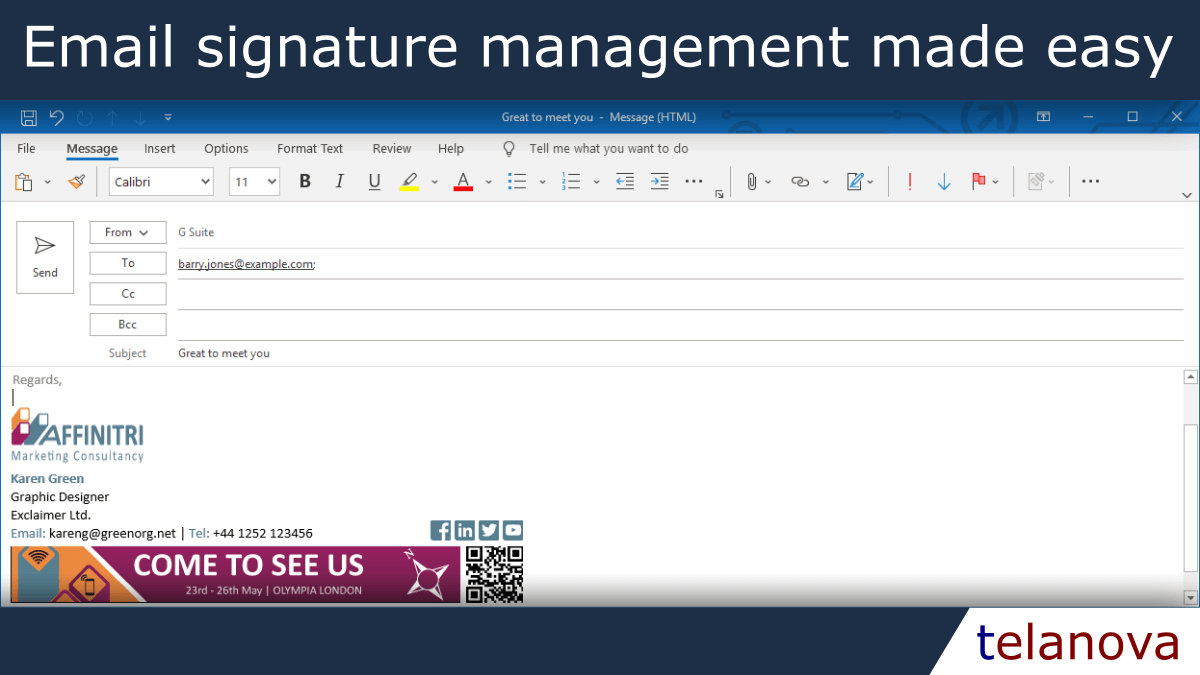
Why Small Businesses Should Use Exclaimer for Email Signatures
By Telanova | 03 September 2025
Designing a Folder/File Sharing Structure for Small and Medium Businesses (SMBs)
By Telanova | 27 August 2025
What the M&S and Co-op Ransomware Attacks Mean for Your Business
By Telanova | 20 August 2025
Why You Still Need to Back Up Cloud Data (Even Microsoft 365 & Google Workspace)
By Telanova | 23 July 2025
Reminder: Only 3 Months Left Until Windows 10 Reaches End of Life
By Telanova | 14 July 2025
What we do to support Microsoft 365 - User Management Email Management
By Telanova | 02 July 2025
How Managed IT Services Can Save Your Small Business Time & Money
By Telanova | 18 June 2025
Outsourced IT Helpdesk vs. In-House Support: Which is Right for Your Business?
By Telanova | 11 June 2025
Why you should ensure your laptops and other mobile devices are encrypted
By Telanova | 23 October 2024
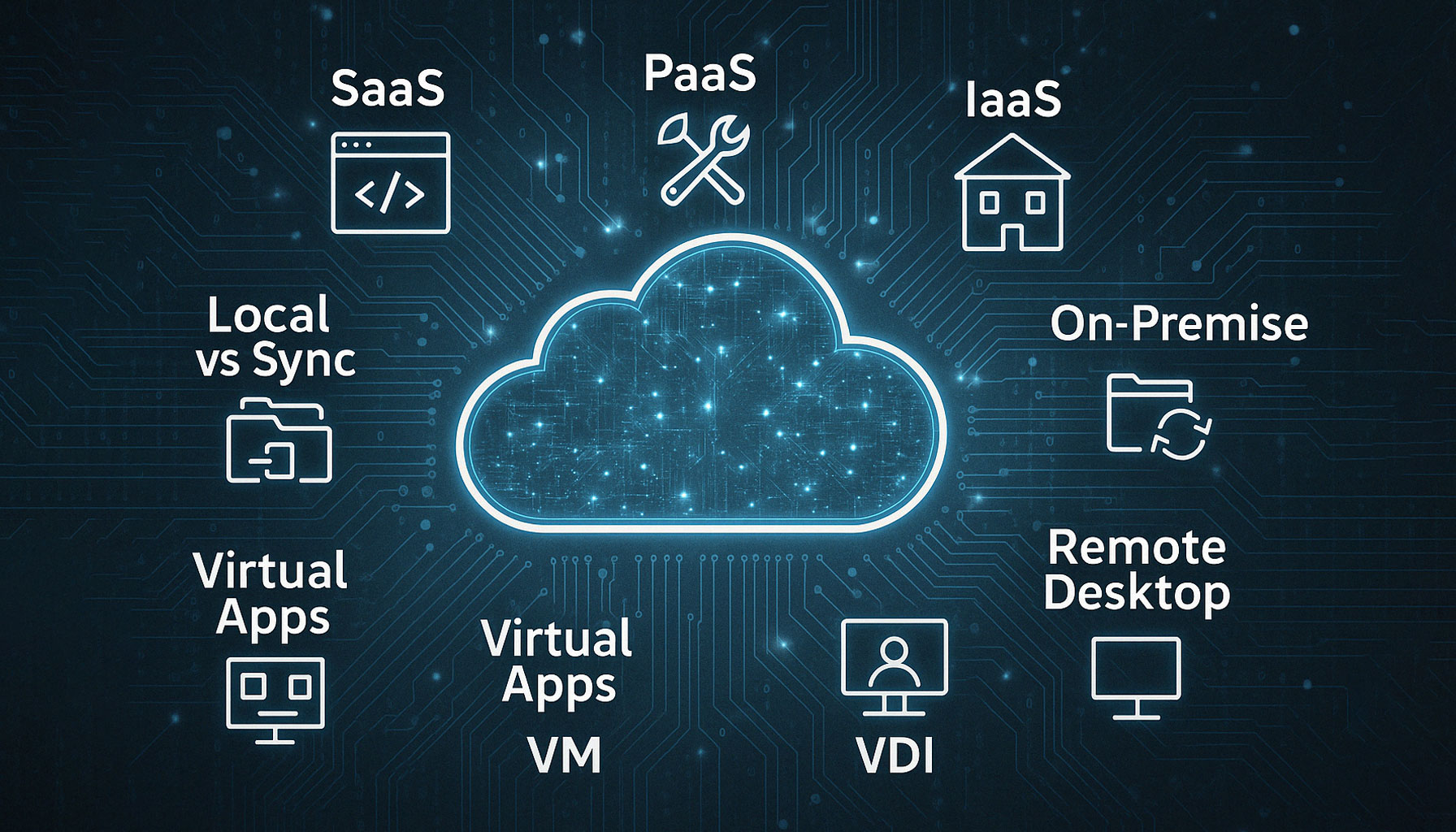
Case Study: Migrating from Cloud Remote Desktop to Pure SaaS for an Ascot-Based Business
By Telanova | 25 September 2024
WiFi or wired connections - How to get the best for your organisation?
By Telanova | 22 May 2022
Discover if WiFi or wired connections is the best for your organisation?Bring Your Own Device safely
By Telanova | 14 March 2022
Discover how to safely enable staff to bring their own devices.